Analysis of APPs Related to COVID19 Using Tacyt (II)
We continue with the research started in the previous entry in which we analysed these type of applications with our Tacyt tool. Regarding the application analysed, we can see that a quick glance at the permissions in Tacyt already makes it clear that we are not dealing with a conventional APP: permissions for calls, accounts, SMS, elimination of processes, NFC, audio recording and a long etcetera.
All this is much more typical of a malicious APP than a legitimate one, whatever its functionality is. The probability of a Trojan running in the background in order to access sensitive information generated via the mobile device is therefore quite high.
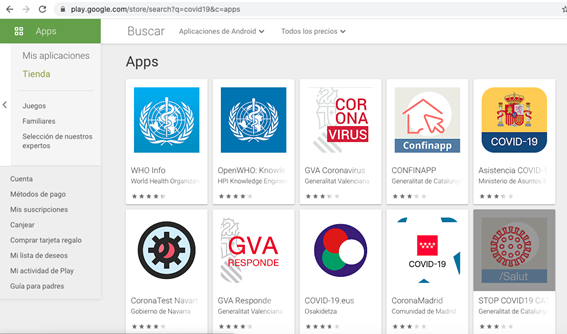 Official Apps in Spain accessible in Google Market (10 altogether)
Official Apps in Spain accessible in Google Market (10 altogether)
Nothing to do with the amount of applications found in any unofficial market:
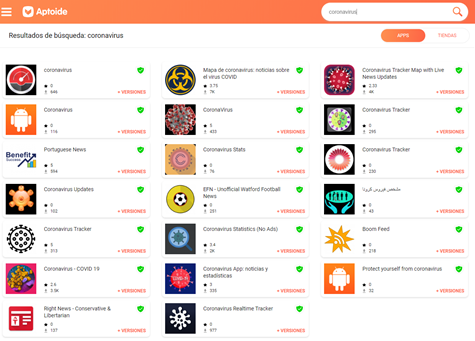 Apps found in APTOIDE, an alternative market using the term: “coronavirus”
Apps found in APTOIDE, an alternative market using the term: “coronavirus”
As with other markets, Aptoide, for example, does not directly download the app we have requested but the “downloader” through which the actual download will be requested. This can easily be guessed by checking that the file size is exactly the same:
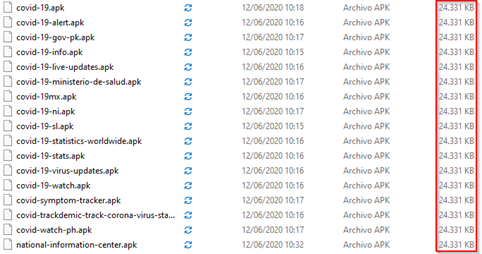 Downloaded Apps through APTOIDE
Downloaded Apps through APTOIDE
In fact, we easily check it out at Tacyt when uploading these applications. It detects them as one, with identical hash:
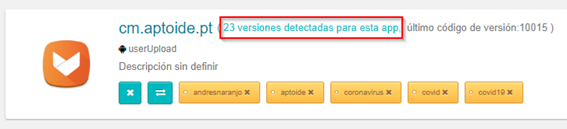
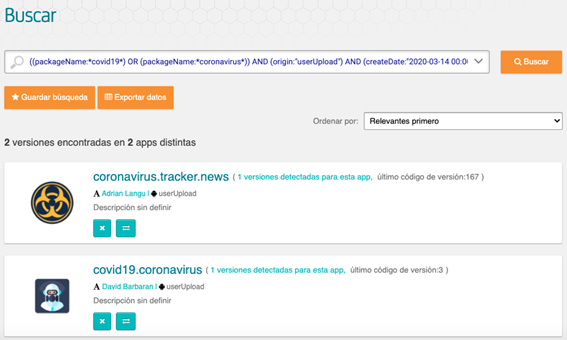
This is due to Tacyt not only including its own application discovery drivers and applications downloading, but also, using the upload function (either via web or API) the user can upload the applications to be analysed. These can be seen labelled as “userUpload” and can also be tagged with our own identification labels (as in the image: the author of the upload or the market from which it was downloaded).
This upload function can be very useful to detect altered versions of our legitimate applications in unofficial markets, for example, from a bank. Tacyt includes a button on the interface to compare applications.
In any case, we do not miss the opportunity to totally discourage the installation of applications from unofficial sources.
Google Play Search Using Tacyt for COVID19 Related Apps Since the Beginning of the Pandemic
We will focus the research on Google Play. The filters are used to form the next search in Tacyt. As you can see these usual composite queries (dorks) in Google search, for example, are easy to read:
((packageName:*covid19*) OR (packageName:*coronavirus*)) AND (origin:"GooglePlay") AND (createDate:"2020-03-14 00:00:00 - today")
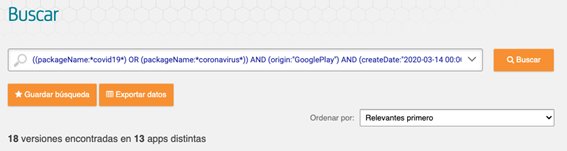 “Dorking” to search using Tacyt apps in Google Play related to COVID-19 published since the beginning of the alarm state
“Dorking” to search using Tacyt apps in Google Play related to COVID-19 published since the beginning of the alarm state
Tacyt’s respond to the previous search:
 Apps related to COVID-19 published overseas in Google Play
Apps related to COVID-19 published overseas in Google Play
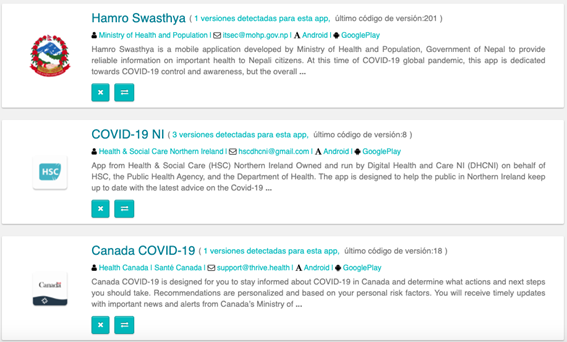
We now search for unofficial apps related to COVID19 using Tacyt from the official date of the start of the pandemic. For this task, we can use the parameter ORIGIN indicating the exclusion of all those whose origin is not the official one. For example -origin:GooglePlay.
((packageName:*covid19*) OR (packageName:*coronavirus*)) AND (-origin:GooglePlay) AND (createDate:"2020-03-14 00:00:00 - today")
 Unofficial apps published since the beginning of the pandemic
Unofficial apps published since the beginning of the pandemic
For example we have a look at the permissions of the app with “coronavirus.tracker.news” package name and do a quick scan.
The following permissions are suspicious: (we only comment on permissions different to the “normal” official apps that violate privacy or security)
android.permission.CHANGE_WIFI_STATE: allows the APP to change the state of Wi-Fi connectivity.android.permission.INTERNET: allows the APP to open network connections.android.permission.WRITE_EXTERNAL_STORAGE: allows the APP to write in the external storage of the device.android.permission.READ_EXTERNAL_STORAGE: allows the APP to read on the external storage of the device.android.permission.WAKE_LOCK: allows you to use PowerManager WakeLocks to prevent the processor from going into sleep mode or the screen from getting dark.
For any research, we can load the apps in batches into Tacyt and then search for them using a custom label and locating, for example, as we said, suspicious permissions:
Likewise, we could have used the expiry date of the certificate (sometimes suspiciously long), apikeys, text or emails chains associated with malware, and a long etc…
We will see in the next part some more information about the findings.
 Hybrid Cloud
Hybrid Cloud Cybersecurity
Cybersecurity AI & Data
AI & Data IoT & Connectivity
IoT & Connectivity Business Applications
Business Applications Intelligent Workplace
Intelligent Workplace Consulting & Professional Services
Consulting & Professional Services Small Medium Enterprise
Small Medium Enterprise Health and Social Care
Health and Social Care Industry
Industry Retail
Retail Tourism and Leisure
Tourism and Leisure Transport & Logistics
Transport & Logistics Energy & Utilities
Energy & Utilities Banking and Finance
Banking and Finance Smart Cities
Smart Cities Public Sector
Public Sector



