Cyber Security Briefing, 19 – 23 June
Critical vulnerabilities in Asus routers
Asus has issued a security advisory addressing a total of nine vulnerabilities affecting multiple router models. Among these security flaws, the one registered as CVE-2022-26376, which is due to a memory corruption in the Asuswrt firmware that could allow threat actors to perform denial-of-service attacks or allow code execution, stands out for its criticality.
The vulnerability registered as CVE-2018-1160 is due to a Netatalk write out of bounds weakness, which could be exploited to allow arbitrary code execution on vulnerable devices. In addition, Asus has indicated that if the new firmware version cannot be installed on the affected devices, it is recommended to disable the services accessible from the WAN side to avoid possible repercussions.
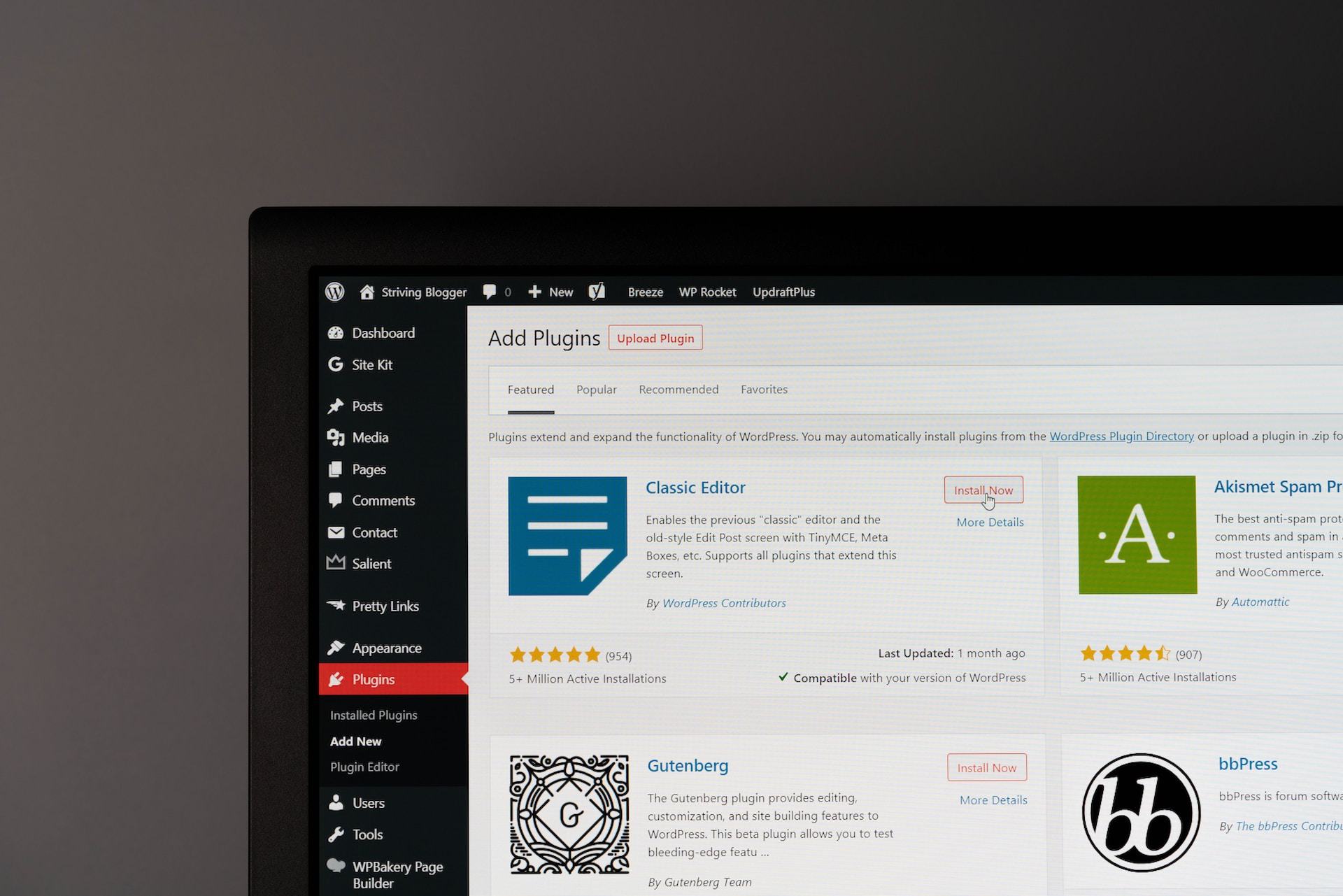
Critical vulnerabilities in WordPress plugins
Researchers at Defiant have identified two critical authentication bypass vulnerabilities in two WordPress plugins with tens of thousands of installations.
On the one hand, there is the security flaw registered as CVE-2023-2986, CVSSv3 of 9.8, which affects Abandoned Cart Lite for WooCommerce. Exploiting this vulnerability could allow malicious actors to log in as customers or access admin accounts and compromise the affected website. However, the issue has been patched in version 5.15.1 of Abandoned Cart Lite for WooCommerce.
On the other hand, there is the CVE-2023-2834 vulnerability affecting the WordPress Booklt plugin. An attacker could exploit this flaw to gain access to any account on the affected website, including the administrator account, knowing only the email address. This issue has been fixed in BookIt version 2.3.8.
Apple patches the two 0-days used in Operation Triangulation
Apple has released an emergency security update to patch the two 0-day vulnerabilities used in Operation Triangulation, as the incident’s discoverer Kaspersky called the campaign. The two vulnerabilities, CVE-2023-32434 and CVE-2023-32435, were exploited in a zero-click attack (receipt of the message triggers the infection without the need for user interaction) against iOS devices via iMessage.
This security update from Apple coincides with Kaspersky’s publication of its final analysis of the so-called Operation Triangulation and the spyware in which it exploits the two 0-days. Kaspersky highlights that it has capabilities to manipulate files, interfere with running processes, exfiltrate credentials and certificates as well as transmit geolocation data, including the device’s coordinates, altitude, speed, and direction of movement.
Microsoft Teams flaw allows malware to be distributed
Researchers at Jumpsec have published the results of an investigation in which they claim to have identified a security flaw in Microsoft Teams that could allow malware to be distributed. Specifically, the experts say they have discovered a way for an account outside the target organisation to bypass the relevant security measures to allow malware to be delivered directly into the inbox.
The attack methodology works in case the victim is running Microsoft Teams with default settings, and the attacker needs to change the internal and external recipient ID in the POST request of a message, thus tricking the system into treating an external user as internal.
This way, when the executable is sent, it is actually hosted on a SharePoint domain and the target downloads it from there. Microsoft acknowledges the problem, but has pointed out that it does not meet the requirements to fix the bug immediately.
New Mirai variant exploits multiple IoT exploits
A variant of the Mirai botnet has been discovered by researchers at Palo Alto Networks Unit 42. The variant targets nearly two dozen vulnerabilities in devices from brands such as D-Link, Arris, Zyxel, TP-Link, Tenda, Netgear and MediaTek, with the aim of using them in DDoS attacks.
The malware has been identified in two ongoing campaigns that started in March and escalated in April and June and targets a total of 22 known security holes in various connected products such as routers, DVRs, NVRs, access control systems, among others. The attack starts by exploiting one of the aforementioned flaws and then downloads a botnet client suitable for the compromised device and directly accesses the encrypted strings, making it difficult to detect.
Unlike other Mirai variants, this one does not have the ability to obtain brute-force login credentials, so it relies on manual exploitation of vulnerabilities by operators. Signs of infection of this botnet on IoT devices include overheating, configuration changes, frequent disconnections, and a general decrease in performance.
 Hybrid Cloud
Hybrid Cloud Cybersecurity
Cybersecurity Data & AI
Data & AI IoT & Connectivity
IoT & Connectivity Business Applications
Business Applications Intelligent Workplace
Intelligent Workplace Small Medium Enterprise
Small Medium Enterprise Health
Health Industry
Industry Retail
Retail Tourism and Leisure
Tourism and Leisure Transport & Logistics
Transport & Logistics Energy & Utilities
Energy & Utilities Banking and Finance
Banking and Finance Smart Cities
Smart Cities Public Sector
Public Sector