Typosquatting: how to detect and protect yourself
Typosquatting is a type of cyberattack that involves creating a domain name that is very similar to that of a well-known, legitimate website with the intention of deceiving users.
This type of misleading domain name can also be used in e-mail addresses to make them appear legitimate to the naked eye, but which are fake.
Typosquatting is a combination of the words "typo" and "squatting".
The attacker can exploit common typos, misspellings or typing errors to carry out the deception. These errors may omit or change the order of letters. They can also substitute characters, replacing visually similar letters. Anything to create a misleading domain name. For example:
- Change an "l" or an "i", the "o" for a "0" (zero) or use "rn" instead of an "m".
- Register the same domain name but with a different extension, such as ".co" instead of ".com".
- Use a domain name with a similar appearance, such as goggle.com instead of google.com
In addition, "in this type of cyber-attacks it is very common to use alternative spellings or words with double spelling and also the use of special characters, such as hyphens", explains Susana Alwasity, Threat Intelligence Team Lead at Telefónica Tech.
In this case, for example:
- If the legitimate domain is bankXonline.com a typosquatting could be bankX-online.com
In either case, the attacker's purpose is to trick users into visiting the fake site believing they are on the legitimate website.
It is from such a website (which may be the same or even a duplicate of the original site) that attackers can distribute apps and malware or steal information such as login credentials, bank card numbers or personal information.
How is typosquatting used in cyberattacks?
Typosquatting is a popular technique used by cybercriminals to launch different attacks, including:
- Phishing attacks: attackers can create a fake login page that looks like the page of a legitimate website. When users type their login credentials into the fake page, the attacker gets hold of them to use them for malicious purposes.
- Malware distribution: Attackers can create a fake website that prompts users to download a file or software. When users download and install that file, they are actually unknowingly installing malware on their computer or device.
- Ad fraud: Attackers can create a fake website that generates advertising revenue by tricking users into clicking on ads. The attacker earns money for each click, even if the ads are irrelevant or harmful.
"In addition to the theft of personal information, which can lead to phishing attacks, typosquatting can also be aimed at redirecting the domain to another destination or blackmail and reputational attacks against companies or individuals," explains Susana.
The case of the Icelandic national pólice
An example of a phishing attack based on typosquatting took place in Iceland in 2018. Then, cyber attackers used a domain name similar to the official domain of the Icelandic national police (Lögreglan, in Icelandic) to deceive citizens.
In this case, the attackers registered a domain that replaced the "l" with an "i" (logregIan.is instead of logreglan.is), making it appear at first glance to be the legitimate domain of the country's police. But it was not.
As in the previous paragraph, in the email the "i" in the URL was capitalised ("I") to make it look like an "l". At first glance, and taking advantage of the fact that our brains sometimes read words that are not words, many recipients did not detect the deception.
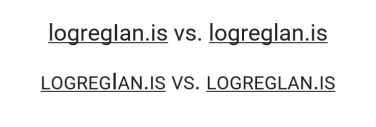 Converting the text to small caps reveals the deception: what looks like a lowercase "L" is actually a capital "i".
Converting the text to small caps reveals the deception: what looks like a lowercase "L" is actually a capital "i".
They then used that domain to create a fake website that looked exactly like the legitimate website. And they sent phishing emails asking the recipient to access that URL and enter personal information.
The full story and analysis of the attack can be found at Police Phishing Attack Targets Bank Credentials.
How to detect and protect yourself from typosquatting?
Often, as in the case of Lögreglan, it is not easy to detect and protect yourself from typosquatting. But following these recommendations from our experts at Telefónica Tech helps to reduce the risk:
- Look at the URL before accessing a website or the sender's email extension when it is an email: look for spelling mistakes or other suspicious elements in both the domain name and its TLD extension (.com, .es,.co...).
- Manually copy and paste the URLs of links received by email: this prevents the malicious destination URL from being hidden under a linked or anchor text.
- If in doubt about what is actually written in a URL or email address, copy and paste it into a text processor such as Word: changing the font helps to detect visual deception because some fonts reveal the differences between characters better than others. It also helps to convert the text to capital letters. Word also detects the language, which is very useful when typosquatting using letters of the Cyrillic alphabet.
 Although they look the same, the letters 'A' and 'J' of the Cyrillic alphabet are different characters from the 'A' and 'J' of the Latin alphabet.
Although they look the same, the letters 'A' and 'J' of the Cyrillic alphabet are different characters from the 'A' and 'J' of the Latin alphabet.
- Use a password manager: password managers automatically enter access or login credentials only on legitimate sites, where the credential was generated.
- Install antivirus software: they are useful for detecting and blocking malicious websites that could be used in typosquatting attacks.
- Don't trust the little padlock 🔒 in the browser bar: at first glance it reveals neither the authenticity of the certificate, nor who it belongs to, nor its intentions.
- Enable two-factor authentication: two-factor authentication adds an extra layer of security, making it harder for attackers to steal login credentials on websites or apps.
- Enable Google Passkeys: This is a Google identification or login method that combines the benefits of password managers and two-factor authentication in the same process.
It is important to check every little detail in a URL and to be suspicious, no matter how small the error may seem. It is advisable to invest time in prevention, as the consequences can be harmful and irremediable. -Susana Alwasity, Telefónica Tech.
How does Google Passkeys protect against typosquatting?
Google Passkeys generates unique and complex passwords for each website the user visits. When the user visits a website, Google Passkeys automatically fills in the login credentials, such as username and password.
With Google Passkeys, there is no need to remember or type the password on apps and websites, minimising the risk of the user mistakenly typing their login credentials on a fake website.
Continuing with the example above, if a user trying to visit google.com mistakenly ends up at goggle.com Google Passkeys will not work because there is a difference in the domain. So it will not automatically enter the login credentials. If this happens, it is best to leave the website, without trying to enter the credentials by hand.
Conclusion
Typosquatting is a cyber threat that can result in identity theft, account theft, financial and reputational loss, or lead to ransomware, among other possible consequences.
Therefore, it is always important to pay attention to URLs and email addresses that may be suspicious or of unknown origin, in order to minimise the risk and protect yourself from this type of cyberattack.
Featured image: Freepik.
 Hybrid Cloud
Hybrid Cloud Cybersecurity
Cybersecurity Data & AI
Data & AI IoT & Connectivity
IoT & Connectivity Business Applications
Business Applications Intelligent Workplace
Intelligent Workplace Small Medium Enterprise
Small Medium Enterprise Health
Health Industry
Industry Retail
Retail Tourism and Leisure
Tourism and Leisure Transport & Logistics
Transport & Logistics Energy & Utilities
Energy & Utilities Banking and Finance
Banking and Finance Smart Cities
Smart Cities Public Sector
Public Sector





