The strategic CISO in the face of quantum risk: cryptographic and PQC capabilities now required
Quantum computing is not a 2035 threat. It is a strategic pressure that security leaders must integrate today into their priorities, their teams and their conversations with the business.
There is a recurring pattern in the history of Cybersecurity: the most disruptive threats are systematically ignored until a case makes the headlines. Ransomware was considered background noise until it paralysed hospitals. Software supply chain risk was theoretical until SolarWinds. Quantum computing remains in that same grey area today, labelled by many security teams as a 'future problem'.
The challenge with this mindset is that the quantum threat will not behave like ransomware. There will be no defining incident to trigger headlines and unlock budgets. The damage, in its most dangerous form, will already have been done before it is detected: encrypted data today can be captured now and decrypted later, when quantum computers become sufficiently powerful. The Harvest Now, Decrypt Later (HNDL) attack does not need to wait for the arrival of Q-Day.
The difference between a reactive CISO and a strategic one, in quantum terms, is three to five years of operational advantage. That window is closing now.
For those in leadership or security roles, a question arises: should quantum already be considered a core capability in their role? The short answer is yes.
The detailed answer is not about becoming a quantum physicist, but about acquiring the capabilities required to manage this risk, communicate the importance of the transition to the Board, start the transition towards post-quantum cryptography, and lead that process.
The impact of quantum technology on the CISO role
Today, the CISO is no longer just a technical guardian. They are a corporate risk manager with a business perspective, a key interface with regulators and a driver of cultural change. The quantum threat requires all three dimensions of the role to evolve simultaneously.
From a technical perspective, the algorithms underpinning virtually all secure digital communications (RSA, ECC, Diffie-Hellman) are vulnerable to Shor’s algorithm when executed on a sufficiently capable quantum computer. NIST has already published the first post-quantum cryptography (PQC) standards: ML-KEM, ML-DSA and SLH-DSA. This is not a future standard, but one already in force that auditors will reference in upcoming cycles.
From a strategic perspective, crypto-agile migration, the ability to replace cryptographic algorithms without redesigning the entire infrastructure, requires architectural decisions that need to be made today, with implications for Cloud provider contracts, HSM hardware lifecycles and API design.
Delaying these decisions creates a cumulative cost.
The six quantum capabilities of the CISO
As noted, this is not about mastering quantum mechanics. It is about being able to contribute meaningfully to decisions where quantum computing is treated as a risk factor.
These are the six capabilities that already distinguish the most advanced CISOs:
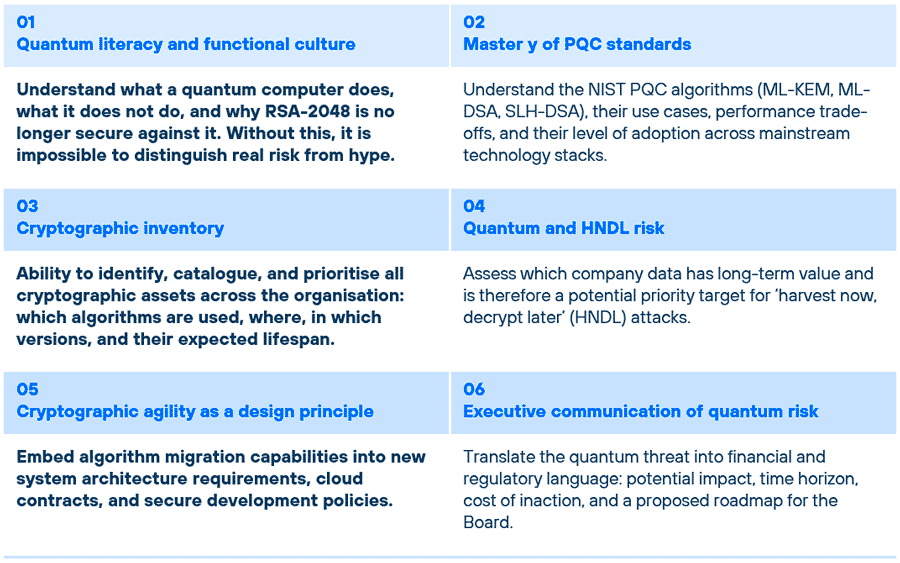
A CISO who does not understand the PQC landscape will not be able to defend their position in an advanced security audit, nor articulate a credible migration plan to the Board.
■ These capabilities are not independent: the cryptographic inventory underpins risk management and incident response; functional literacy enables executive communication; and crypto-agility turns risks into concrete actions.
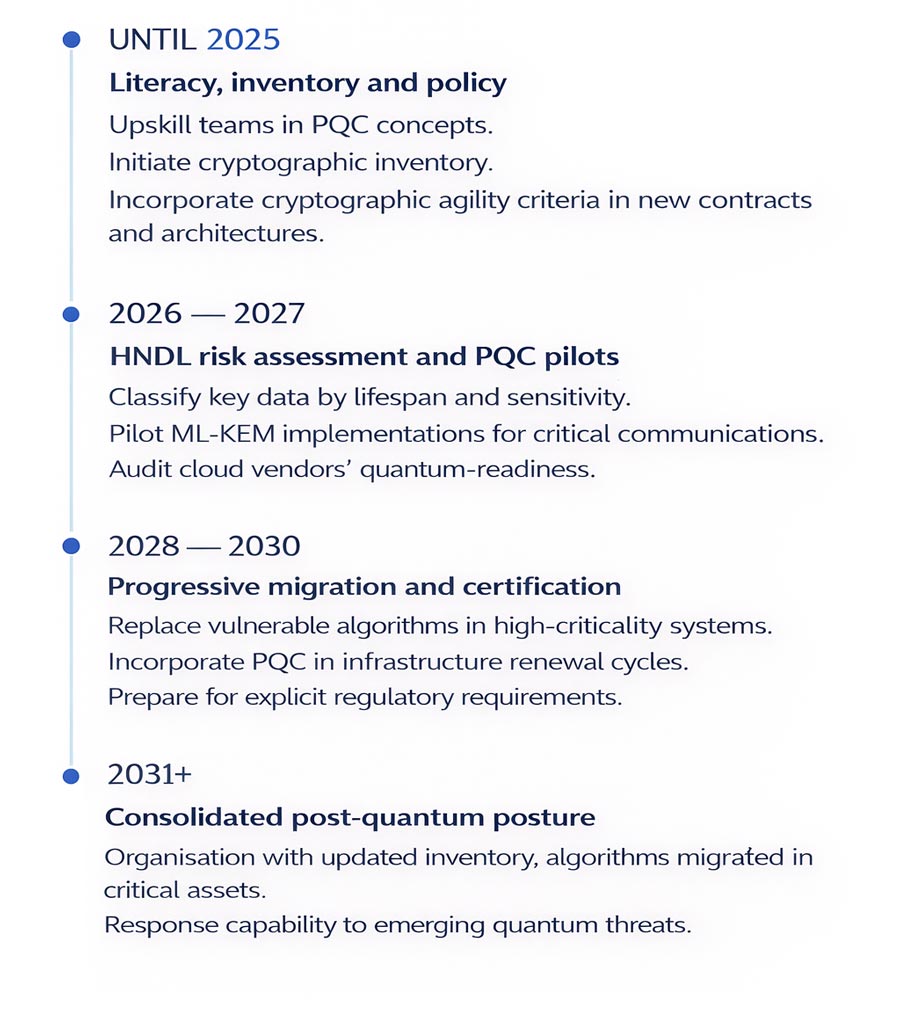
The timeline: when each capability matters
A common objection is: if Q-Day is five, ten or fifteen years away, why act now?
The answer lies in understanding that cryptographic migration is not an event, it is a process with a minimum duration of five to eight years in medium and large organisations. You need to start before you need it.
The team: what profiles does the CISO need alongside them?
The CISO does not need to be the organisation’s quantum expert. But they do need to know which profiles to hire or outsource, and how to assess the quality of that expertise. At present, the post-quantum security talent market is scarce and fragmented. Organisations that are training internal PQC professionals today will have a competitive advantage in the 2027 talent market.
The most relevant profiles to build internal quantum capability are:
- Security architects with a background in applied cryptography.
- PKI engineers with experience in key infrastructure renewal.
- GRC and privacy consultants specialising in cryptography and with knowledge of emerging quantum-related regulatory frameworks: NIST, DORA, NIS2, PCI, ENISA, CCN-CERT in Spain.
■ Outsourcing and partnerships with technology integrators are a valid strategy, particularly for the initial cryptographic inventory phase and HNDL risk assessments, which require specialised methodologies that few organisations currently have in-house.
Bringing quantum to the Board of Directors
Probably the most undervalued capability is also the most critical: the ability to make quantum risk understandable and actionable for a Board that already has many competing priorities.
The common mistake is to present quantum computing as a technical issue. It is not. It is a business continuity, regulatory compliance and long-term information asset management issue.
An effective Board-level argument has three elements: a realistic risk horizon, the cost of inaction versus the cost of the migration programme, and an action plan with verifiable milestones that does not require solving everything at once.
It is not about the Board understanding qubits. It is about understanding the risk to its most critical assets.
The risk of waiting
Corporate inertia is the greatest ally of the quantum threat. Infrastructure renewal cycles, migration timelines for legacy systems, team upskilling, vendor negotiations… everything takes longer than expected. Organisations that begin their quantum transition in 2027 will be operating against both the regulatory and technological clock.
The CISO who develops quantum capabilities today not as an exotic specialisation, but as a natural extension of risk management will be better positioned to lead that transition when external pressure arrives. And it will.
 ■ We invite you to download our complimentary handbook Strategic preparation for Post-Quantum Cryptography and start as soon as possible the transition towards a resilient cryptographic infrastructure ready for the quantum era.
■ We invite you to download our complimentary handbook Strategic preparation for Post-Quantum Cryptography and start as soon as possible the transition towards a resilient cryptographic infrastructure ready for the quantum era.
A crypto-agility-based approach enables systems to adapt to new threats without compromising current operations.
______
 Hybrid Cloud
Hybrid Cloud Cybersecurity
Cybersecurity Data & AI
Data & AI IoT & Connectivity
IoT & Connectivity Business Applications
Business Applications Intelligent Workplace
Intelligent Workplace Small Medium Enterprise
Small Medium Enterprise Health
Health Industry
Industry Retail
Retail Tourism and Leisure
Tourism and Leisure Transport & Logistics
Transport & Logistics Energy & Utilities
Energy & Utilities Banking and Finance
Banking and Finance Smart Cities
Smart Cities Public Sector
Public Sector





