Cryptography, a tool for protecting data shared on the network
Cyber Security is nowadays an essential element in companies. However, new ways of undermining it are emerging every day. Many have asked themselves: how can companies securely store their data, how can credit card information be protected when making online purchases? The answer to these questions is cryptography.
Cryptography becomes vital, especially when there are so many computer security risks, such as spyware or social engineering.
That is why the vast majority of websites employ it to ensure the privacy of their users. In fact, according to projections by Grand View Research (2019), from 2019 to 2025, the global encryption software market is expected to grow at an annual rate of 16.8%.
How can cryptography be defined?
This term is defined as the art of converting data into a format that cannot be read. In other words, messages containing confidential information are encrypted. This prevents unscrupulous people from accessing data that could be breached. Such encrypted data is designed with a key that enables access (Onwutalobi, 2011).
To encrypt a message, the sender must manipulate the content using some systematic method, known as an algorithm. The original message, called plain text, can be encoded so that its letters are aligned in an unintelligible order, or each letter can be replaced by another letter. This is known as ciphertext.
Why should cryptographic systems be used?
1. They can be used in different technological devices
Both an IPhone and an Android device, for example, can have their own encryption methods depending on the needs of the companies.
Likewise, it is possible to encrypt content on an SD card or USB memory stick. There are several possibilities, you just have to find the most appropriate method.
2. Working remotely is more secure
Organizations today often need to work securely when their employees communicate remotely. A 2018 North American Report published by Shred-It revealed that vulnerability risks are higher when working in this way. Therefore, working collaboratively through data encryption will prevent information from falling into the wrong hands.
3. Cryptography protects privacy
t is frightening to think how exposed data can be in companies. According to an article by Hern (2019) published in The Guardian newspaper, in 2018 more than 770 million emails and passwords were exposed. All of this resulted from vulnerabilities in accessing individual data. Therefore, data encryption can prevent sensitive details from being unknowingly published on the Internet.
4. Provides a competitive advantage
Providing companies with cryptographic support for their various sources of information and data will give customers greater peace of mind. Organizations are aware of the essentials of this procedure. A study by the Ponemon Institute (2019) revealed that 45 % of businesses have cryptography strategies. Less than 42% have limited data encryption strategies for certain applications or types of data.
Types of encryption
The two most popular ways to apply cryptography are: shared secret key encryption and public key encryption, also known as symmetric and asymmetric encryption systems, respectively (Vasquez, 2015).
Shared-key encryption
Also known as symmetric. It consists of using the same key for encryption and decryption. Any user who has this key can receive the message.
This method is fast and can be used for a large volume of data. It is also used with block cipher chaining, which is subject to a key and an initialization vector. All this to form a cipher from a series of data block.
The user who wishes to decrypt the message will have to possess the key and initialization vector. Often used with public key encryption because of its vulnerability.
Public key encryption
Also called asymmetric encryption, it uses two different keys that share a mathematical link. In other words, one key is used for encryption (private key) and another for decryption (public key).
The public key can be shared between recipients. The other key is kept only by the originator of the message. Its computational cost is high. Finally, cryptography opens the opportunity for companies to strengthen the security of their customers. This will consolidate their reputation and further commitment to innovations around the latest technologies.
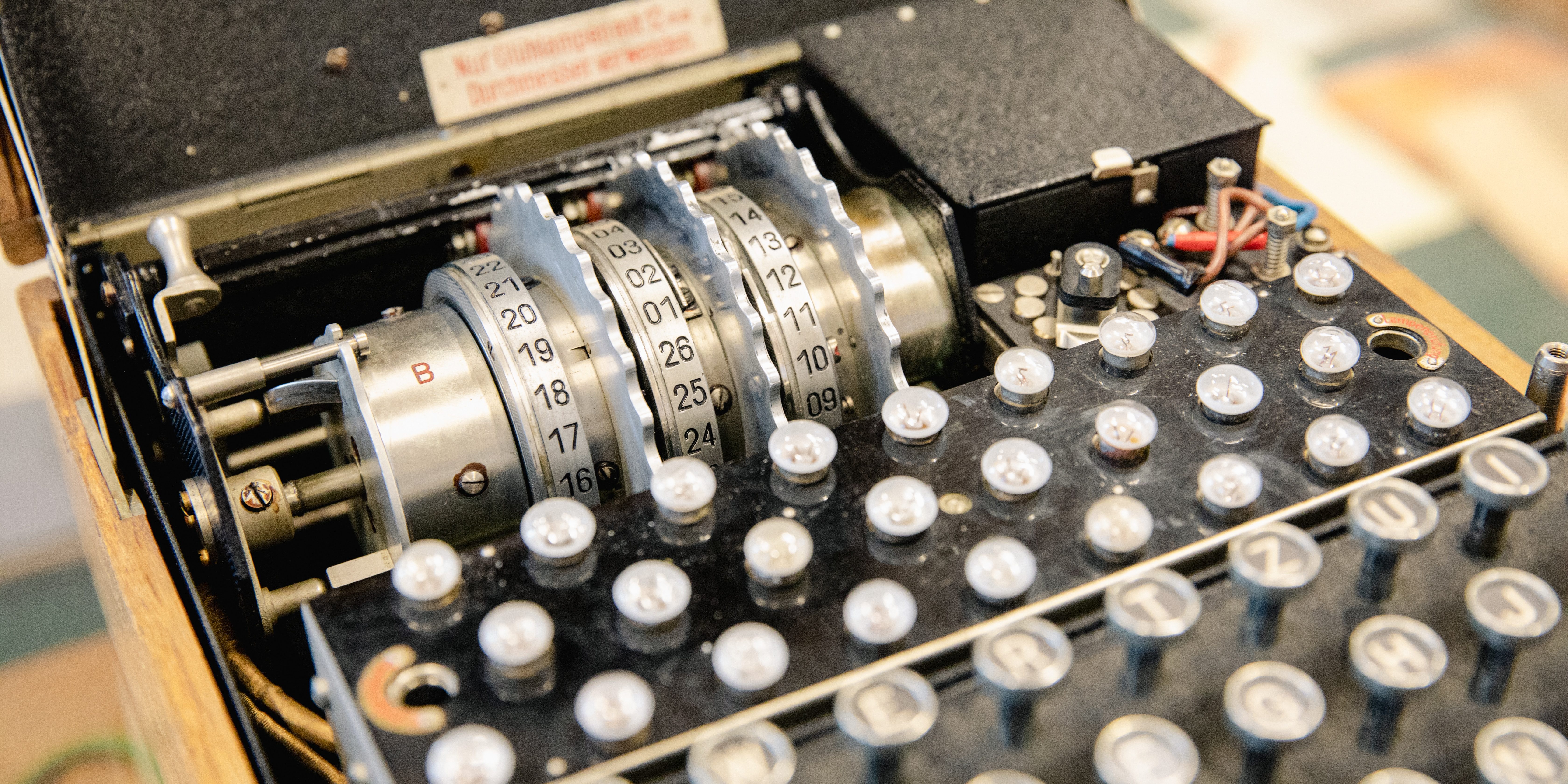
Featured photo: Christian Lendl / Unsplash
 Hybrid Cloud
Hybrid Cloud Cybersecurity
Cybersecurity Data & AI
Data & AI IoT & Connectivity
IoT & Connectivity Business Applications
Business Applications Intelligent Workplace
Intelligent Workplace Small Medium Enterprise
Small Medium Enterprise Health
Health Industry
Industry Retail
Retail Tourism and Leisure
Tourism and Leisure Transport & Logistics
Transport & Logistics Energy & Utilities
Energy & Utilities Banking and Finance
Banking and Finance Smart Cities
Smart Cities Public Sector
Public Sector