OT Cybersecurity: zero trust
TABLE OF CONTENTS
- Introduction
- A long road: the challenge of implementing Zero Trust in OT
- Old standards, new models: the evolution of the Purdue model
- More than a guide of recommendations
1. Introduction
No one will be surprised if we say that the world is not exactly going through one of the calmest or most peaceful moments in its history. International tensions affect consumption, markets, geography, raw materials and technology. Cybersecurity is no exception and the major global actors are well aware of it.
In this context, it is becoming critical to update, strengthen and reinforce strategies that enhance Cybersecurity in all its dimensions.
Against this backdrop, the United States Department of War (DoW), formerly the Department of Defense (DoD), worked throughout 2025 to strengthen Cybersecurity by broadly implementing a strategy focused on Zero Trust policies (DTM-25-003). As part of this strategy, on November 18 a guide was published defining the Zero Trust policy for OT environments.
Naturally, the Zero Trust for Operational Technology guide, a 28 page document, builds on the foundations created by the strategy mentioned above as well as other frameworks, such as the Cybersecurity reference framework published by the DoD itself in 2023 and the OT security guide published by NIST, NIST SP 800-82.
If guides from NIST or CISA are already considered essential reading for the global Cybersecurity ecosystem, when the military enters the conversation the level of interest rises quickly.
2. A long road
Zero Trust is not just another strategy. It represents a paradigm shift in the way access is conceived. It is not about a blacklist. Not even about a whitelist. It is about distrusting by default any activity that cannot justify itself. This approach carries risks that in the IT ecosystem have been mitigated with great care, allowing the adoption of Zero Trust to move forward steadily.
However, the OT ecosystem is different. In a world where, as I have mentioned in other articles and talks, the principle of “if it works, do not touch it” is older than computing itself, adopting a paradigm shift that introduces a high level of operational risk generates resistance, cold sweats and a mistrust that is not easy to overcome.
This point, the specific adoption of Zero Trust for OT, is one of the first aspects addressed in the document we are analysing. It acknowledges that a set of activities and impacts related to the Zero Trust policy has been reviewed to facilitate its implementation in OT environments and that this information considers the different approaches and requirements of these environments.
Zero Trust in OT represents a paradigm shift.
Not surprisingly, the basic principles cited in the document, strong authentication, network segmentation and threat monitoring, are applicable to this environment, but they require a very measured approach because operational constraints tend not to offer second chances.
3. Old standards, new models
While it is true that implementing Zero Trust in OT environments requires adaptation, it also seems necessary to adapt long standing standards in this domain to align them with this policy. The DoW proposes adjusting these frameworks to make implementation easier. The reasoning is clear: typical architectures based on layered models have clearly defined boundaries between them. Measures associated with the Zero Trust policy are far more dynamic and would clash with such compact and well defined architectures, a direct legacy of the ecosystem they originate from.
In this regard, the proposal is to take the well known five layer Purdue model, from level 0 to level 4, and transform it into two layers: the Operational Layer and the Process Control Layer.
- The Control Layer would include levels 0, 1 and 2 of the Purdue model, covering instrumentation such as sensors and actuators, basic controllers such as PLC or RTU devices and the supervisory layer including HMI systems or engineering workstations.
- The Operational Layer would include levels 3, including 3.5, and 4. Some elements from level 2 are also incorporated into this layer, such as operator workstations (OWE or OWS). Including these level 2 elements helps soften the abrupt separation we previously described in the Purdue layered model.
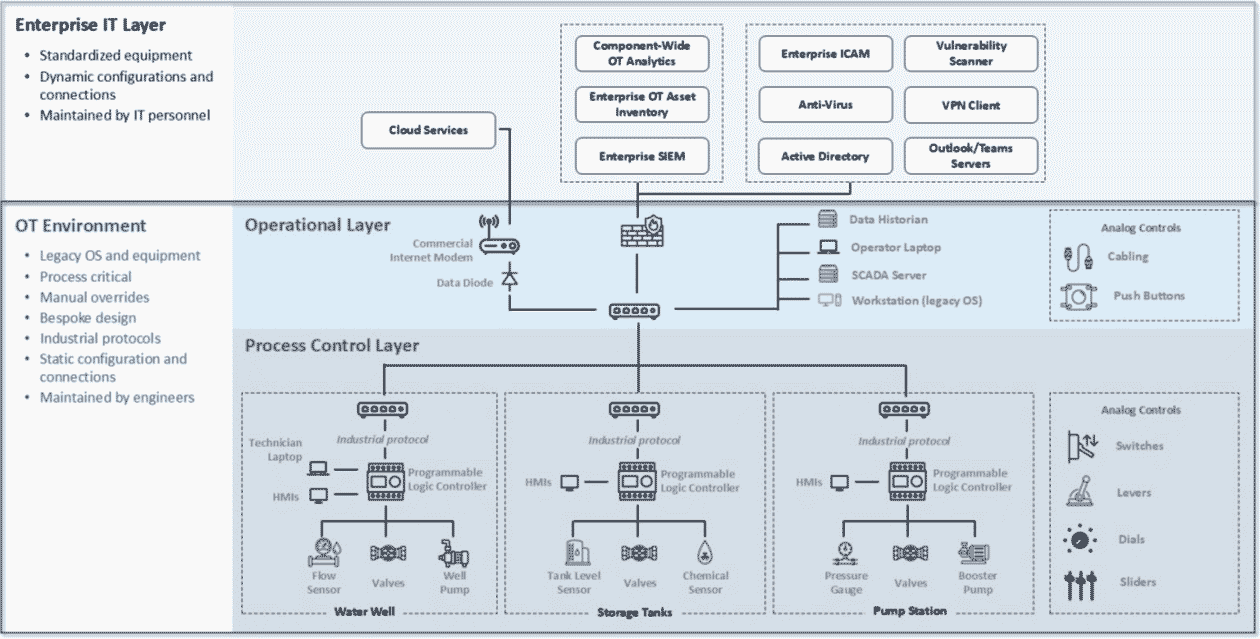 Proposed new layers and interaction between IT and OT ecosystems. Source: DoD USA
Proposed new layers and interaction between IT and OT ecosystems. Source: DoD USA
Adapting the Purdue model is key to applying Zero Trust in OT.
4. More than a guide of recommendations
A large part of the document details several “pillars”, along with their associated activities, that are relevant to implementing Zero Trust in the OT ecosystem according to the previously mentioned guides and standards. By reading them, we can identify where an agency like this wants to place particular emphasis, something worth paying attention to. We will comment on only a few of them here, since this article is not intended to be an exhaustive analysis of the document.
The guide defines concrete pillars for implementing Zero Trust across the OT ecosystem.
4.1 The importance of data
In this pillar, the DoW highlights the importance of maintaining continuous monitoring and correlation to enable active cyber threat detection. Basic elements for data and alert management are mentioned, such as SIEM platforms or orchestration tools. The document also stresses the importance of enriching data and using OT specific information sources to generate high quality CTI (Cyber Threat Intelligence). This is where our Aristeo platform can help.
4.2 Automation, but with safeguards
The guide also notes that although automating actions is recommended to achieve immediate responses to threats, the human factor remains essential. References to having alternative response paths, human oversight during automated processes and verification and review mechanisms appear repeatedly throughout the document. This reflects the critical nature of the OT ecosystem, especially in environments important enough to attract the attention of the DoW, where control and recovery mechanisms for operational processes are essential. Something similar to the redundancy built into critical aircraft systems.
4.3 Security for EoL and future generations
Another point repeatedly mentioned is the importance of knowing how to manage devices and components at the end of their lifecycle (end of life). The reason is simple: today’s OT environments may look very different from those of tomorrow. We do not know exactly how or when, but we do know that components will be replaced, new ones will arrive and the environments themselves will evolve.
For the DoW, the Zero Trust policy must transcend these changes. This makes sense if we consider the amount of time, money and resources required to implement it.
4.4 Nothing is ever secure enough
Cybersecurity is a dynamic concept. What is secure today may be insecure tomorrow. For this reason, the DoW recommends continuously reassessing implemented measures and dynamically adjusting controls and metrics. In this way, the level of Cybersecurity will always remain optimal, or at least will move in that direction.
The document references inventories, audits and simulations, all well known practices in the Cybersecurity landscape.
4.5 Socratization is the way. Recognising the limits of the OT ecosystem
Plato, in his “Apology of Socrates”, wrote a phrase supposedly spoken by Socrates during the trial that would lead to his death: “An unexamined life is not worth living”. For Socrates, a life without introspection, self reflection and critical thinking was an empty life. Understanding our own limits helps us better understand who we are and how we can improve. Something very similar happens when analysing the security of OT environments.
Although we have left it for the end, this is the most important aspect, which is why it is mentioned almost from the beginning of the document. In the OT universe, different rules apply than in the IT universe. We are almost finishing the article with the same phrase we nearly started with: if it works, do not touch it. Legacy devices, protocols that predate the internet, systems so finely tuned over time that replacing old components with new ones becomes extremely difficult.
—For example, something as basic as encryption can in some cases be unrealistic, since there will be elements and protocols within an OT network that simply do not support it. And we have not even mentioned passwords beyond a basic PIN, if that is even allowed.
These parts of the OT ecosystem should not be treated as exceptions to compliance with Zero Trust policies or any other. They must be accepted as natural components of these environments and addressed with techniques that allow them to be brought under the umbrella of 21st century Cybersecurity.
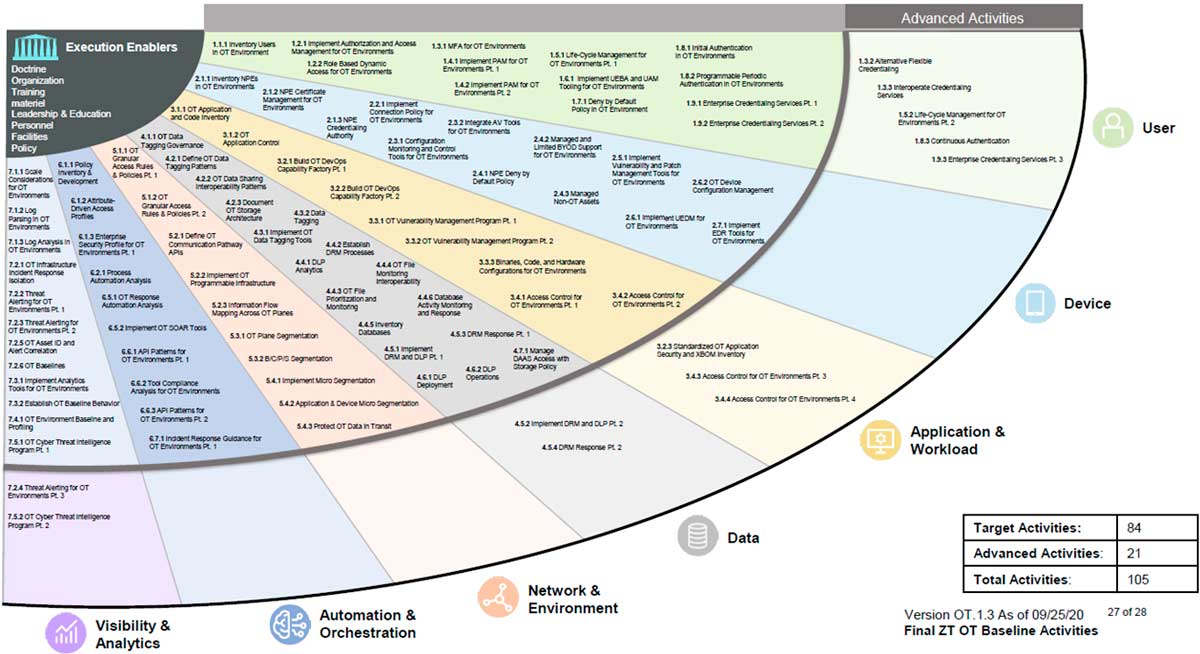
Finally, we leave you with the fan shaped chart summarising all the activities detailed in the document. Nevertheless, we recommend reading it in full.
 Hybrid Cloud
Hybrid Cloud Cybersecurity
Cybersecurity Data & AI
Data & AI IoT & Connectivity
IoT & Connectivity Business Applications
Business Applications Intelligent Workplace
Intelligent Workplace Small Medium Enterprise
Small Medium Enterprise Health
Health Industry
Industry Retail
Retail Tourism and Leisure
Tourism and Leisure Transport & Logistics
Transport & Logistics Energy & Utilities
Energy & Utilities Banking and Finance
Banking and Finance Smart Cities
Smart Cities Public Sector
Public Sector





